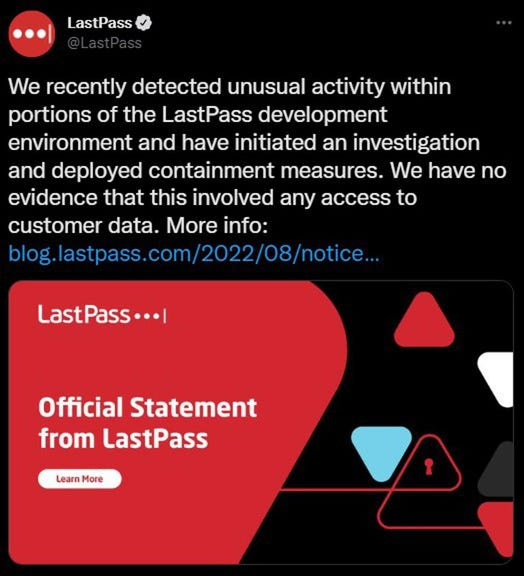
LastPass released its initial statement about the breach on the company’s blog. The LastPass breach was claimed that be limited to their development environment and that no customer information or users’ password vault data had been compromised. However, the company said that it had “engaged a leading cybersecurity and forensics firm,” and its investigation was ongoing.
Password managers are a great way to keep secure, varied credentials on all of your different accounts. They let you log in and out of your favorite sites without having to worry about forgetting all those confusing strings of letters, numbers, and different capitalization.
What happens when a hacker breaches that massive log of data? That nightmare REALLY HAPPENED for LastPass users. If you have the browser extension or app, you’ll want to read on!
Table of Contents
How Did the LastPass Breach Happen?
In the unfortunate case of LastPass, a developer’s account was actually compromised first. Although it’s never fun to have your accounts hacked, choosing a developer for a target gave the hacker immediate access behind the scenes.
What did they do with that access? Well, regular users may be able to take a breath of relief. The hacker targeted the development side of the app, stealing source code and other propriety information. They say that no user information has been compromised, including Master Passwords that would put their credentials and the entire information vault at risk.
Their Zero-Knowledge security model means that even LastPass developers and higher-ups don’t have access to your Master Password, thus this breach wouldn’t put that information in harm’s way.
What About Your Future Security?
LastPass responded to the breach, writing on their blog, “In response to the incident, we have deployed containment and mitigation measures, and engaged a leading cybersecurity and forensics firm. While our investigation is ongoing, we have achieved a state of containment, implemented additional enhanced security measures, and see no further evidence of unauthorized activity.”
The good news is that there was no evidence of malware or some exploitation of the software which could harm your encrypted password vault. Most sources, both inside and apart from LastPass, suggest that there’s no real need to change your passwords, but if you’re feeling uneasy, you can change your Master Password (you should do this anyway, just like it’s recommended to change any other password every three months or so if you don’t have two-factor authentication and a complex, unique password). Click here to learn about Malware Analysis.
You might also consider switching to a password manager with open-source coding, as it will have more transparency in how it works and thus more eyes out for potential vulnerabilities.
3 Open Source Alternatives to LastPass
Open-source password managers offer an alternative solution by allowing users to host their own password databases or use decentralized solutions. These alternatives typically offer similar features as LastPass, including auto-filling login credentials, generating strong passwords, and syncing data across different devices.
One popular open-source alternative to LastPass is KeePass, which is available for Windows, macOS, and Linux. KeePass allows users to store passwords and sensitive information in a local database that is encrypted using advanced encryption algorithms. KeePass also offers features such as two-factor authentication and integration with web browsers.

Another open-source option is Bitwarden, which offers a cloud-based solution that is hosted on the user’s own server or on Bitwarden’s servers. Bitwarden encrypts data at the client-side using AES-256 encryption, ensuring that only the user has access to their data. Bitwarden also offers features such as two-factor authentication and integration with popular web browsers.

Another notable open-source password manager is Password Safe, which offers a local solution that stores passwords in an encrypted database file. Password Safe offers features such as password generation, auto-filling login credentials, and integration with web browsers.
Conclusion
Whatever you decide to do, one thing is clear: The better you understand how your technology and services work, the smarter decisions you can make about your own online security.
References
- https://www.howtogeek.com/828674/lastpass-just-had-a-security-breach/
- https://nakedsecurity.sophos.com/2022/08/29/lastpass-source-code-breach-do-we-still-recommend-password-managers/
- https://www.computerweekly.com/news/252524346/LastPass-breach-limited-in-scale-and-well-managed-say-experts
- https://www.lastpass.com/security/zero-knowledge-security
- https://www.businessinsider.com/guides/tech/how-often-should-i-change-my-password
- https://devops.com/is-open-source-more-secure-than-closed-source/